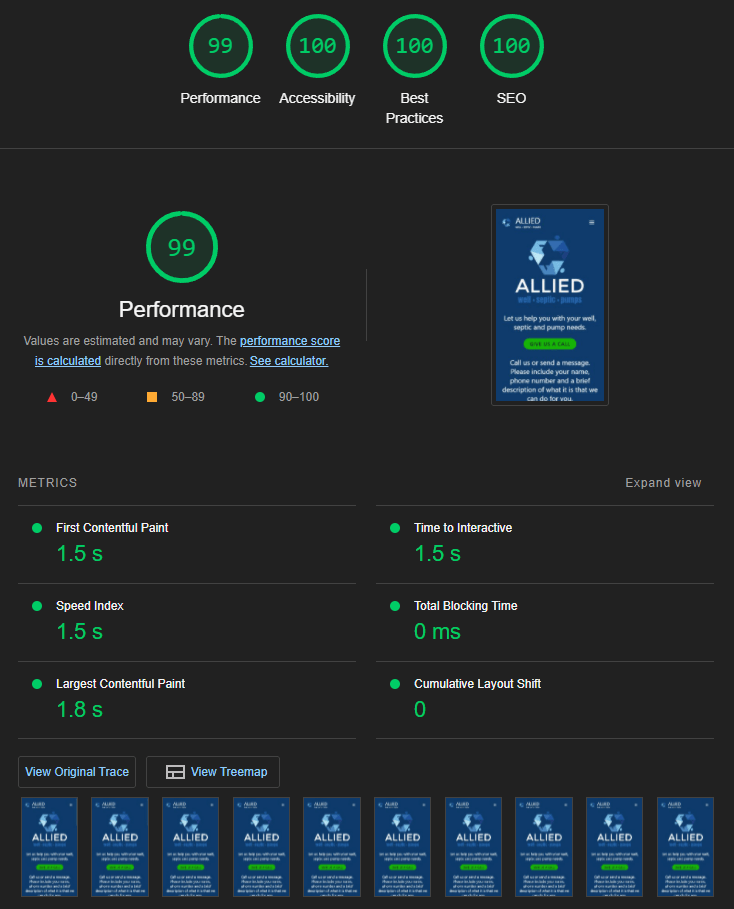
Allied Well, Septic & Pumps created with Astra theme for WordPress
I created a small website for a local contractor that does well drilling in Waupaca, WI. This is the same company that installed our replacement septic system in Waupaca about 6 or 7 years ago. It is surprising how many small companies still do not have a web presence. The company still shows up on […]
Allied Well, Septic & Pumps created with Astra theme for WordPress Read More »